Popularizing some SSRF Techniques for Fun And Profit
Server Side Request Forgery
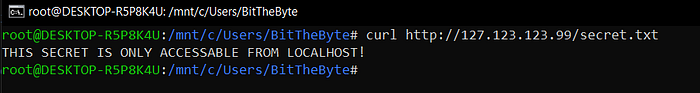
“ Server Side Request Forgery (SSRF) is a type of attack that can be carried out to compromise a server. The exploitation of a SSRF vulnerability enables attackers to send requests made by the web application, often targeting internal systems behind a firewall.” — Detectify
1) DNS Rebinding
This is my favorite type of SSRF they are usually under the cover and most developers don’t know about it. let’s imagine that you’re building a website for HTML to PDF conversion.

1) WEBSITE-DNS
WEBSITE: What is myserver.com IP Address?
DNS: myserver.com IP Address is 123.123.123.123
WEBSITE: OK2) WEBSITE-WEBSITE
WEBSITE: IS 123.123.123.123 Blacklisted?
WEBSITE: NO
WEBSITE: Send GET request to http://myserver.com/file.html3) WEBSITE-DNS
WEBSITE: What is myserver.com IP?
DNS: myserver.com IP Address is 123.123.123.123
WEBSITE: OK4) WEBSITE-USER
WEBSITE: Here is your PDF with the content of http://(123.123.123.123)/file.html
looking at this pseudo code we found that the server checks the domain IP against blacklist before continuing execution. At first glance, this seems to be secure but the truth is it’s not :)
The Domain Name System (DNS) is a hierarchical and decentralized naming system for computers, services, or other resources connected to the Internet
In order to the website server to know your server IP address, it has to perform DNS request and parse the response which looks like this.
root@DESKTOP-R5P8K4U:~# dig myserver.com; <<>> DiG 9.11.3-1ubuntu1.7-Ubuntu <<>> myserver.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 2232
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1452
;; QUESTION SECTION:
;google.com. IN A;; ANSWER SECTION:
myserver.com. 85 IN A 123.123.123.123;; Query time: 124 msec
;; SERVER: 1.0.0.1#53(1.0.0.1)
;; WHEN: Wed Jan 15 16:23:49 EET 2020
;; MSG SIZE rcvd: 55
Now the website server knows that your server has the IP (123.123.123.123)
Back to our example. we know now that we need a way to trick the server to believe that our website IP is not blacklisted and fetch it. In other words what if we set myserver.com IP to legit IP (123.123.123.123) then when the server finished we set it to (169.254.169.254)? that way we could access the EC2 IP and bypass the checks. That is exactly what DNS rebinding is.
Using Python I’ve coded small DNS server which did this task
So the conversation as follows:
1) WEBSITE-DNS
WEBSITE: What is myserver.com IP Address?
DNS: myserver.com IP Address is 123.123.123.123
WEBSITE: OK2) WEBSITE-WEBSITE
WEBSITE: IS 123.123.123.123 Blacklisted?
WEBSITE: NO
WEBSITE: Send GET request to http://myserver.com/file.html3) WEBSITE-DNS
WEBSITE: What is myserver.com IP?
DNS: myserver.com IP Address is 169.254.169.254
WEBSITE: OK4) WEBSITE-USER
WEBSITE: Here is your PDF with the content of http://(169.254.169.254)/file.html
We have successfully bypassed the checks
3) TLS Poison
Original work at https://github.com/jmdx/TLS-poison
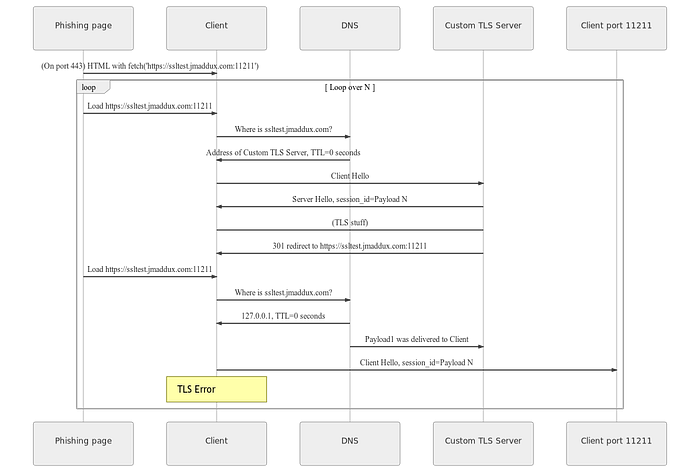
Everything is being discussed at the Github page
2) IPv6
Internet Protocol version 6 (IPv6) is the most recent version of the Internet Protocol (IP), the communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet.
IPv6 is the new sexy, some developers don’t care about IPv6 which led to some interesting behaviors.
2.1) Creating a subdomain with only IPv6 entry ( empty IPv4 ) usually causes trouble with blacklisting.

2.2) Creating a subdomain with (IPv6=0:0:0:0:0:ffff:7f00:1, IPv4=123.123.123.123) as showed before program/lib A might not act the same as program/lib B. Older programs tend to use IPv4 by default however some new programs support both IPv6 and IPv4.
2.3) it’s the same as 2.2 but in reverse (IPv6= 0:0:0:0:0:ffff:7b7b:7b7b, IPv4=127.0.0.1).
2.4) Hybrid IPv6 and DNS Rebinding. I discovered this while pen-testing against a private program and it was the most powerful technique I ever use. I’ll not be providing a code for this but use your imagination to mix between these attacks
Bonus: